Advanced SAP CPI Integration Patterns for Enterprise Cloud Landscapes
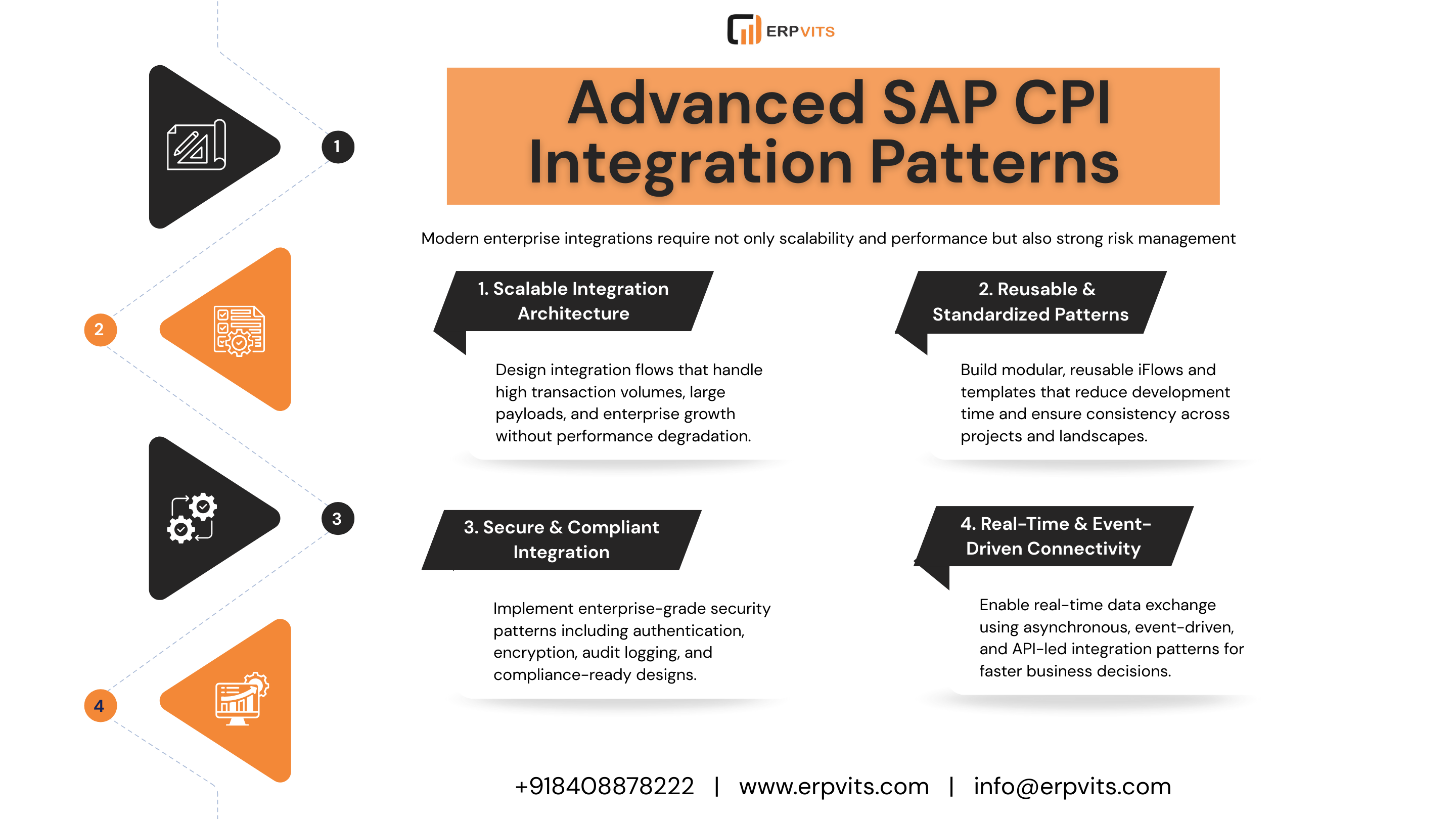
Enterprise environments require reliable, scalable connections between cloud and on-premises systems. SAP Cloud Platform Integration (SAP CPI) provides a structured way to build these connections using established integration patterns — reusable solutions to common challenges in connecting disparate systems.
This article outlines the core integration patterns used in SAP CPI deployments, their practical applications, and the considerations professionals should understand when designing or maintaining enterprise integration landscapes.
What Are SAP CPI Integration Patterns?
Integration patterns are proven, repeatable approaches to solving specific connectivity and data exchange problems. In SAP CPI, they cover everything from basic message delivery to complex multi-system orchestration.
Core Pattern Categories
- Messaging Patterns: Publish-subscribe, request-reply, fire-and-forget, guaranteed delivery
- Routing Patterns: Content-based routing, recipient lists, dynamic routing, message filtering
- Transformation Patterns: Message mapping, data normalization, enrichment, format conversion
- Orchestration Patterns: Sequential processing, parallel execution, aggregation, splitting
- Error Handling Patterns: Exception management, retry mechanisms, dead-letter queues, compensation logic
- Security Patterns: Authentication, authorization, encryption, digital signatures
Using established patterns rather than custom point-to-point integrations reduces technical debt, improves maintainability, and creates a foundation that can scale with business growth.
Why Pattern-Based Integration Matters at Scale
For large organizations, integration architecture decisions have broad consequences. A poorly designed integration can affect downstream processes across multiple business units. Pattern-based development reduces this risk by applying solutions that have been tested in comparable scenarios.
Operational Advantages
- Reusable components lower long-term development and maintenance costs
- Standardized approaches speed up onboarding and project delivery
- Proven error-handling logic improves system reliability
- Built-in compliance and audit capabilities support governance requirements
- Modular designs allow architectures to adapt without full rewrites
Handling Large Payloads in SAP CPI
Large payload management is one of the more technically demanding aspects of enterprise integration. Files exceeding several megabytes, or bulk transfers containing thousands of records, can cause memory issues, timeouts, and network strain if handled incorrectly.
Recommended Approaches
- Message Splitting: Divide large datasets into smaller chunks that can be processed independently and reassembled
- Stream Processing: Enable continuous data flow without loading entire payloads into memory
- Pagination: Retrieve large datasets from source systems in controlled portions
- Asynchronous Queue-Based Processing: Prevent large payloads from blocking other integration flows
Building Reusable Integration Patterns
Reusability is central to sustainable integration development. It begins with identifying common requirements across projects and designing solutions that can be parameterized for different use cases.
Modular iFlows — where components such as authentication handlers, logging mechanisms, and error processors are built as shared artifacts — allow teams to import and reuse logic across multiple integration scenarios. Template-based development provides pre-configured flows for frequent use cases, such as employee data synchronization between SAP S/4HANA and SuccessFactors.
Externalizing configuration through properties files and value mappings ensures that the same integration pattern can be deployed consistently across development, testing, and production environments without code changes.
Message Routing and Transformation
Routing and transformation are foundational capabilities in any enterprise integration platform. SAP CPI supports a range of approaches suited to different business requirements.
Routing Techniques
- Content-based routing using XPath, JSONPath, or Groovy expressions
- Recipient list patterns for delivering messages to multiple destinations
- Failover routing to maintain availability when primary systems are unavailable
- Load balancing across multiple backend systems
- Rate limiting and throttling to control message flow
Transformation Strategies
- Structural conversion between source and target formats using message mapping
- Data enrichment by calling external services or reference databases
- Format conversion between XML, JSON, EDI, and proprietary formats
- Normalization of data from heterogeneous sources
- Complex transformation logic using XSLT, Groovy, or JavaScript
Error Handling and Exception Management
Robust error handling is essential in production integration landscapes. Failures can originate from network issues, authentication problems, data validation errors, or unavailable backend systems. Each type requires a different response strategy.
Exception Hierarchy
Errors should be categorized and handled according to their type:
- Technical Errors: System failures that typically require immediate operational alerts
- Functional Errors: Business rule violations that may require manual review and resolution
- Transient Errors: Temporary connectivity issues suited to automated retry with exponential backoff
Key Error Handling Mechanisms
- Dead-Letter Queues: Capture failed messages for analysis and reprocessing rather than discarding them
- Compensation Patterns: Enable partial rollbacks when one step in a multi-system transaction fails
- Circuit Breaker Pattern: Prevent cascade failures when downstream systems become unavailable
- Monitoring Integration: Use SAP Cloud ALM or equivalent tools to track error patterns and system health
Security Patterns in SAP CPI
Securing integration flows requires layered controls across authentication, data protection, and governance. A single security mechanism is rarely sufficient for enterprise requirements.
Authentication and Authorization
- OAuth 2.0: Token-based API access with scope control and token lifecycle management
- Certificate-Based Authentication: Mutual TLS using X.509 certificates for system-to-system communications
- SAML-Based SSO: Single sign-on for user-driven integration scenarios
- API Key Management: Structured rotation and lifecycle processes to prevent unauthorized access
- Role-Based Access Control (RBAC): Restricting access to integration artifacts based on user roles
Data Protection
- End-to-end payload encryption using GPG or PGP for sensitive data
- SSL/TLS for secure transport layer communications
- Data masking to protect personally identifiable information (PII)
- Tokenization for financial and payment data
- Secure credential storage using CPI security materials
Governance and Compliance
- Audit trails for tracking data access and modifications
- Digital signatures for message integrity verification
- GDPR-aligned data retention and deletion policies
- Encryption key lifecycle management including rotation schedules
API-Led Integration Architecture
API-led integration organizes connectivity into three distinct layers, each with a defined responsibility. This separation makes enterprise architectures easier to maintain and evolve over time.
| Layer | Purpose | Key Responsibilities |
|---|---|---|
| System API | Direct backend connectivity | Data extraction, protocol mediation (SOAP, REST, OData, RFC), system-level error handling |
| Process API | Business process orchestration | Cross-system transaction coordination, business rule enforcement, data aggregation |
| Experience API | Consumer-facing interfaces | Channel-specific formatting (mobile, web, IoT), API gateway integration, version management |
Transport Management and Version Control
Deployment reliability depends heavily on how integration artifacts are managed across environments. Version control using Git repositories, combined with structured branching strategies and CI/CD pipelines, reduces manual errors and supports consistent promotion through development, QA, and production.
Key practices include configuration externalization so that the same artifact can be deployed across environments without code modification, rollback strategies for failed deployments, and blue-green deployment patterns for zero-downtime releases. Change tracking provides audit trails that support both compliance and troubleshooting.
Summary
SAP CPI integration patterns provide a structured framework for building enterprise integration landscapes that are reliable, maintainable, and scalable. Understanding these patterns — from message routing and transformation to error handling, security, and API-led architectures — is essential for professionals working in SAP integration roles.
Applying pattern-based development consistently across projects reduces technical debt, improves system reliability, and creates integration architectures that can accommodate business change without requiring significant rework.
For professionals looking to develop or deepen expertise in SAP CPI, formal training programs that cover these patterns in practical, enterprise-relevant scenarios provide a solid foundation for both implementation and architectural work.
